1Password for SSH & Git
SSH without the headache
Create and configure SSH keys, right in 1Password. Securely store, sync, and access them with the built-in SSH agent. Authorize SSH connections with biometrics – and even sign your Git commits.
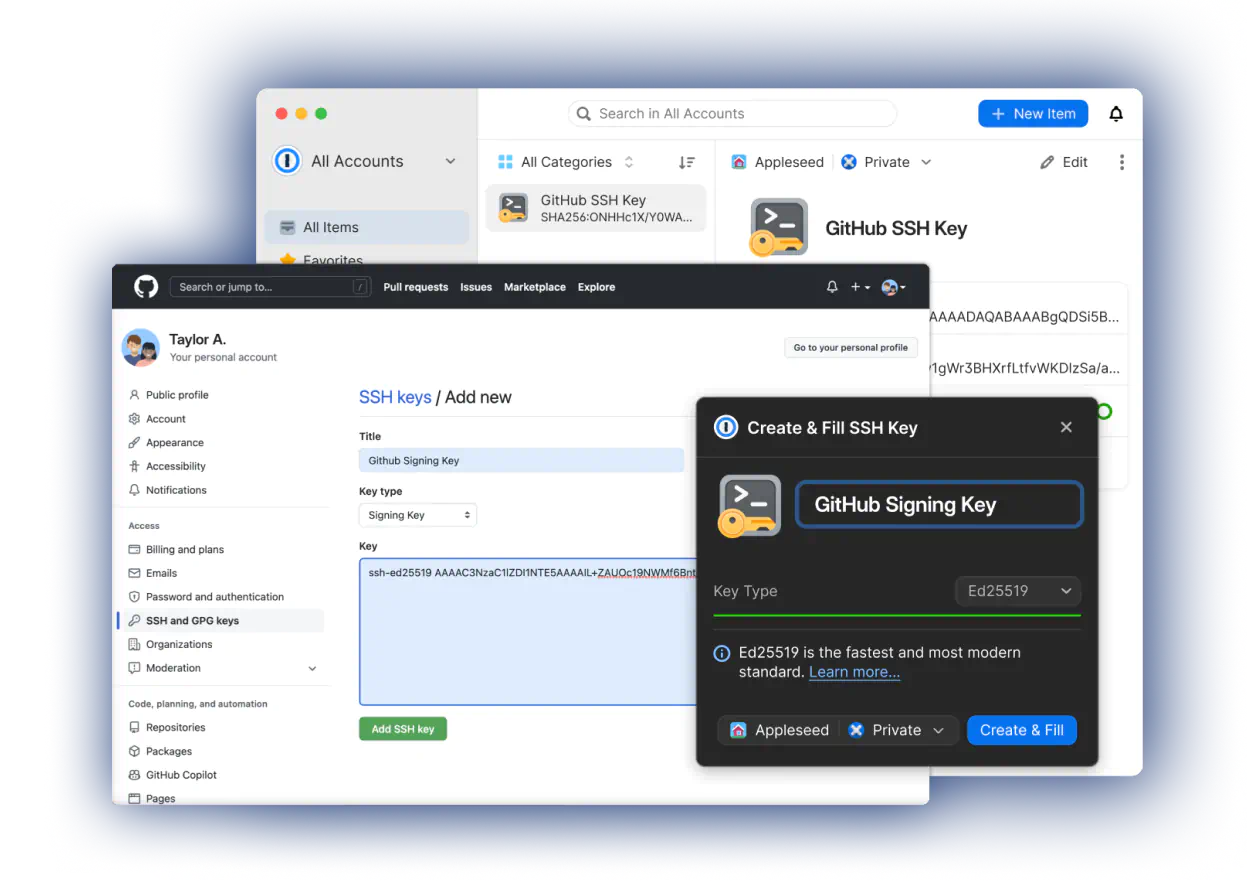
Your SSH keys, made easy
Humans are the weakest link in the chain and are often the target by malicious actors. By migrating your SSH keys to 1Password you are ensuring a smaller attack surface and saving yourself from having to type a (likely weak) password every time you need to sign a Git commit or connect over SSH.
Simon Sickle, Android software engineer at Square
Read more in “1Password Meets Git”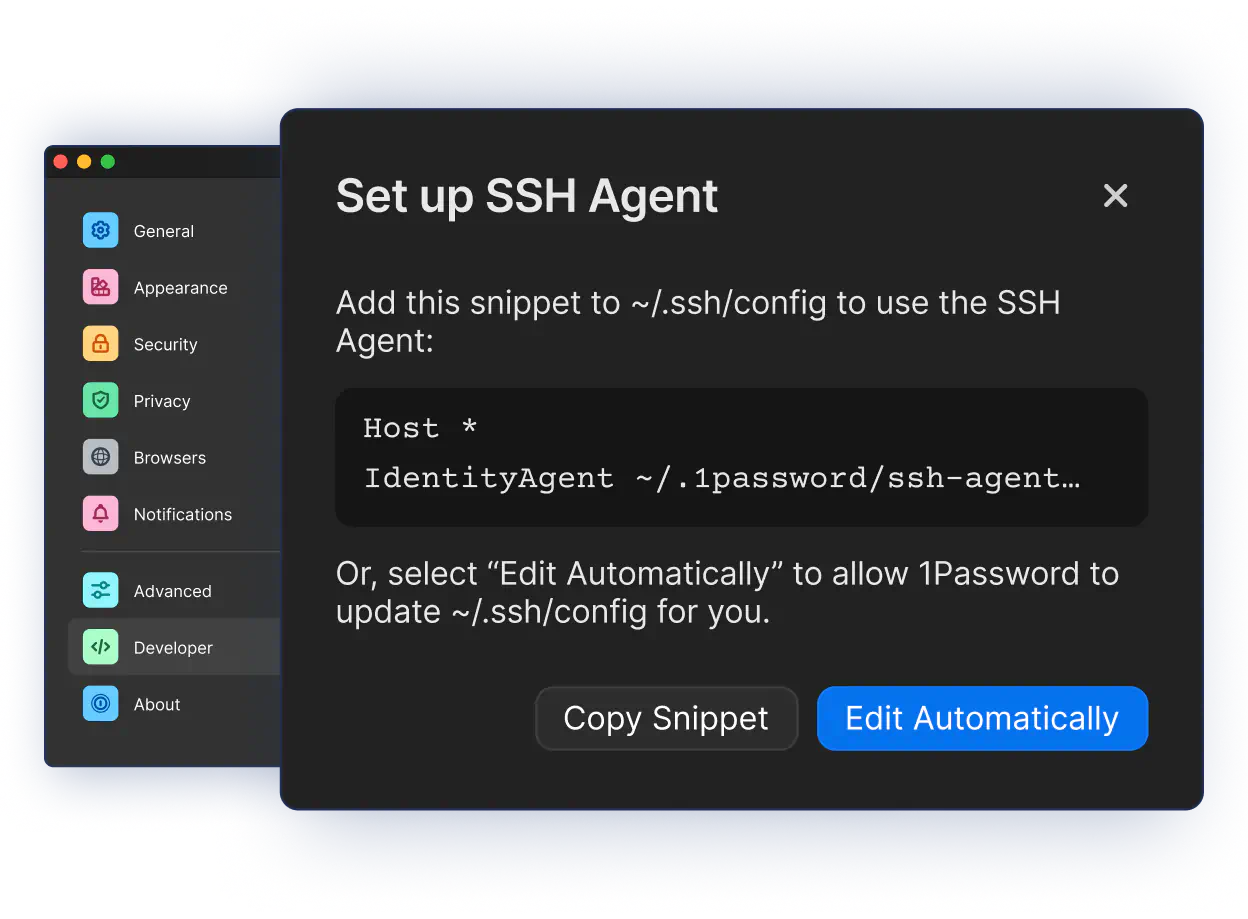
Integrate with your existing SSH workflows
Compatible with dozens of clients
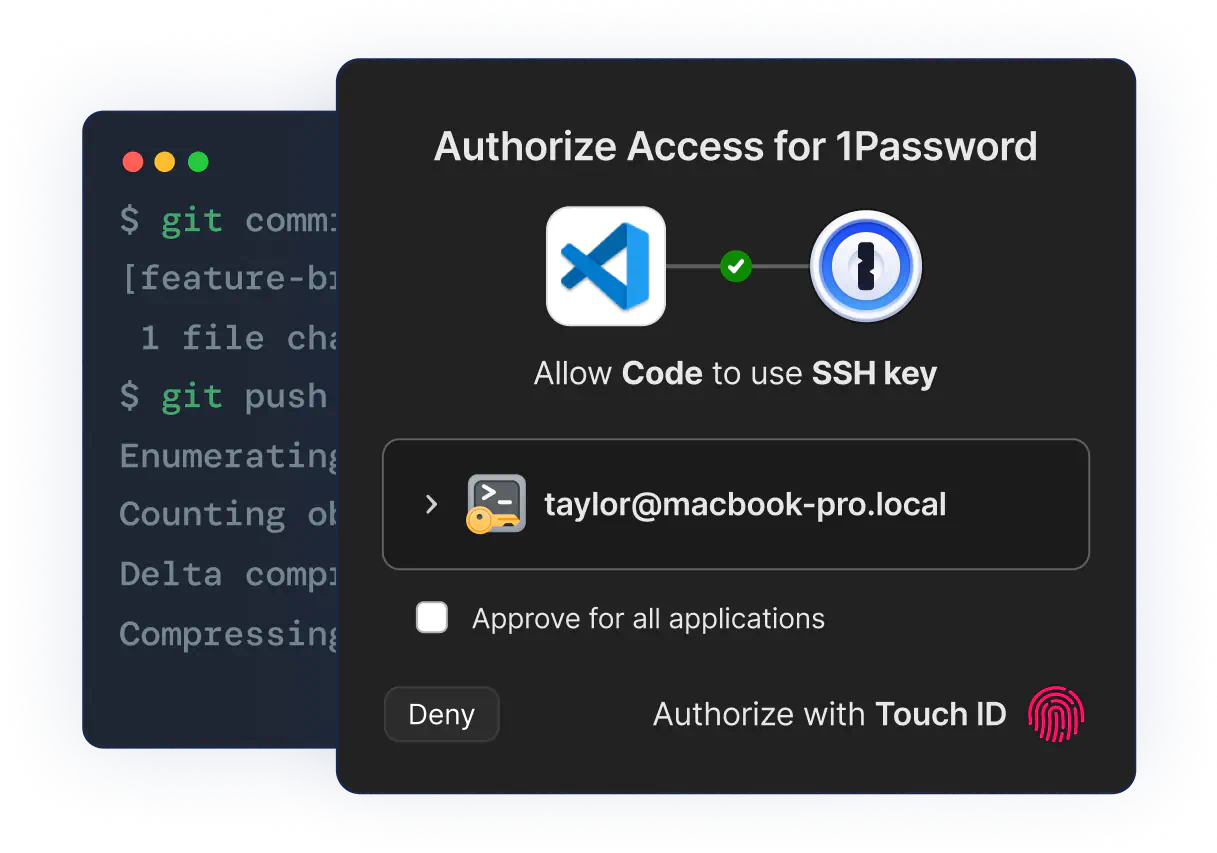
Sign Git commits with your fingerprint
I store my SSH key in 1Password and use it for both Git + SSH and commit signing. Signing SSH private keys meant I don’t have to bother with GPG. Every tool that wants access for auth or signing triggers a Touch ID prompt for 24 hour access. I’m pretty happy with the setup.
Georges Haider on X
View Post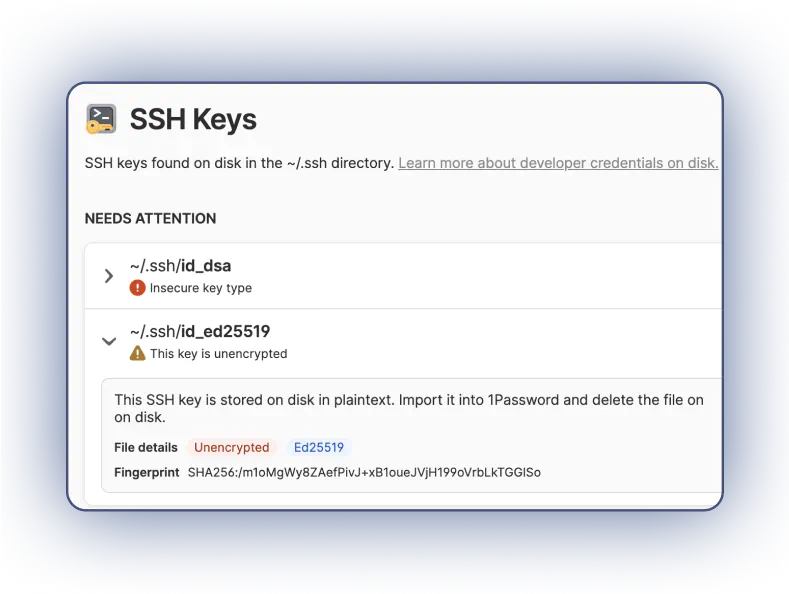
Mitigate security risks from SSH keys stored on your local disk
Find and import SSH keys from your local SSH directory and save them in 1Password for safekeeping.
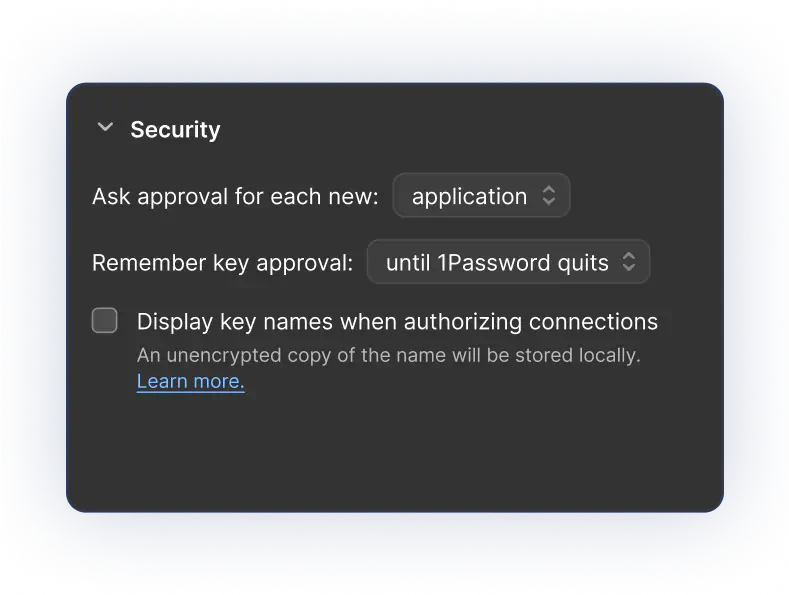
Define how and when SSH keys are accessed
Configure when an application can ask for access to a given key, and how long it should remember that approval, with advanced security settings.
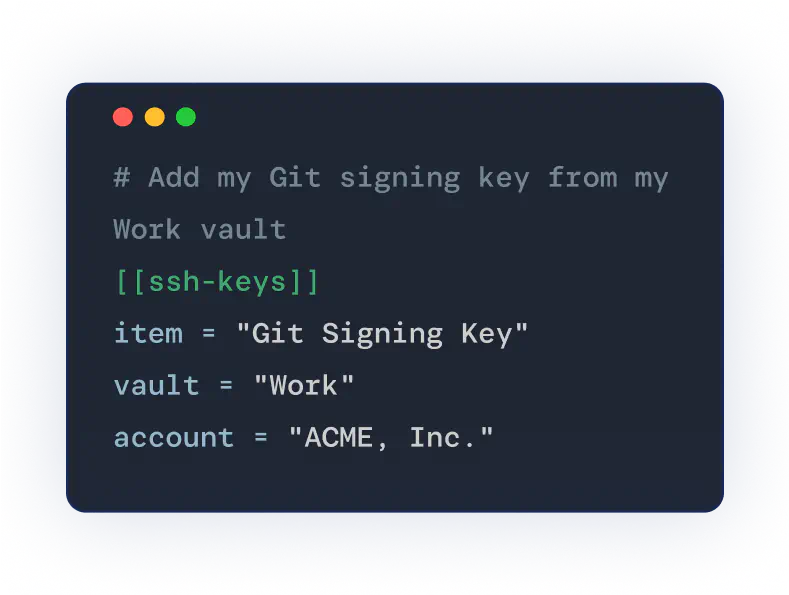
Control SSH key order and location
An agent config file allows you to choose the keys to use on that machine, and the order in which to use them, from any vault.