Discover, secure, and audit access beyond traditional tools
Make identity security match how work actually happens
Modern identity systems were designed for authentication at login. They verify identity once, assign permissions, and assume trust carries forward. That model no longer matches reality.

API keys, tokens, service accounts, and secrets now power developer and agent workflows.

New applications are provisioned outside standard workflows, and credentials are shared beyond SSO.

AI agents generate API keys, call services, access data, and make runtime decisions.
Extended Access Management is delivered through three core pillars
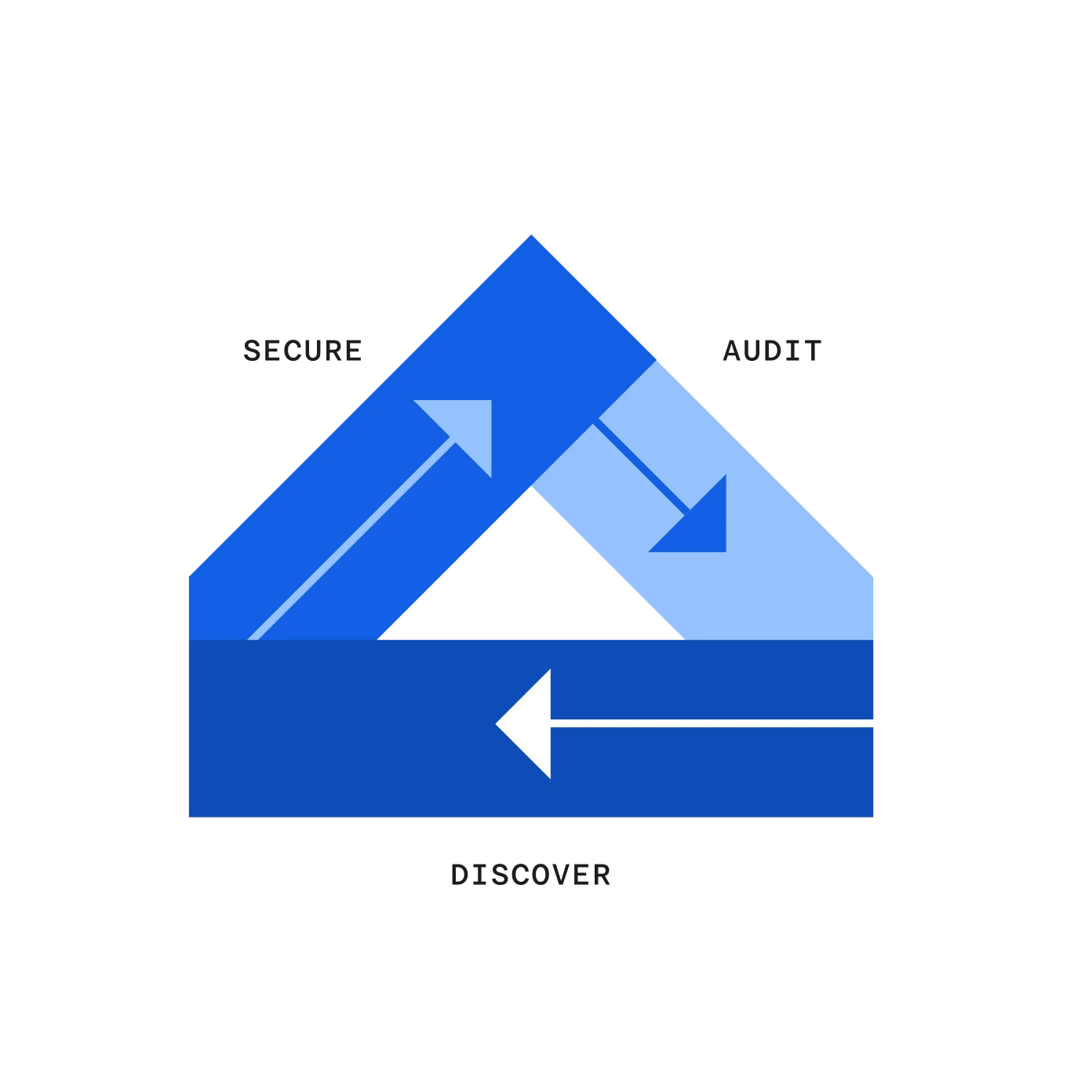
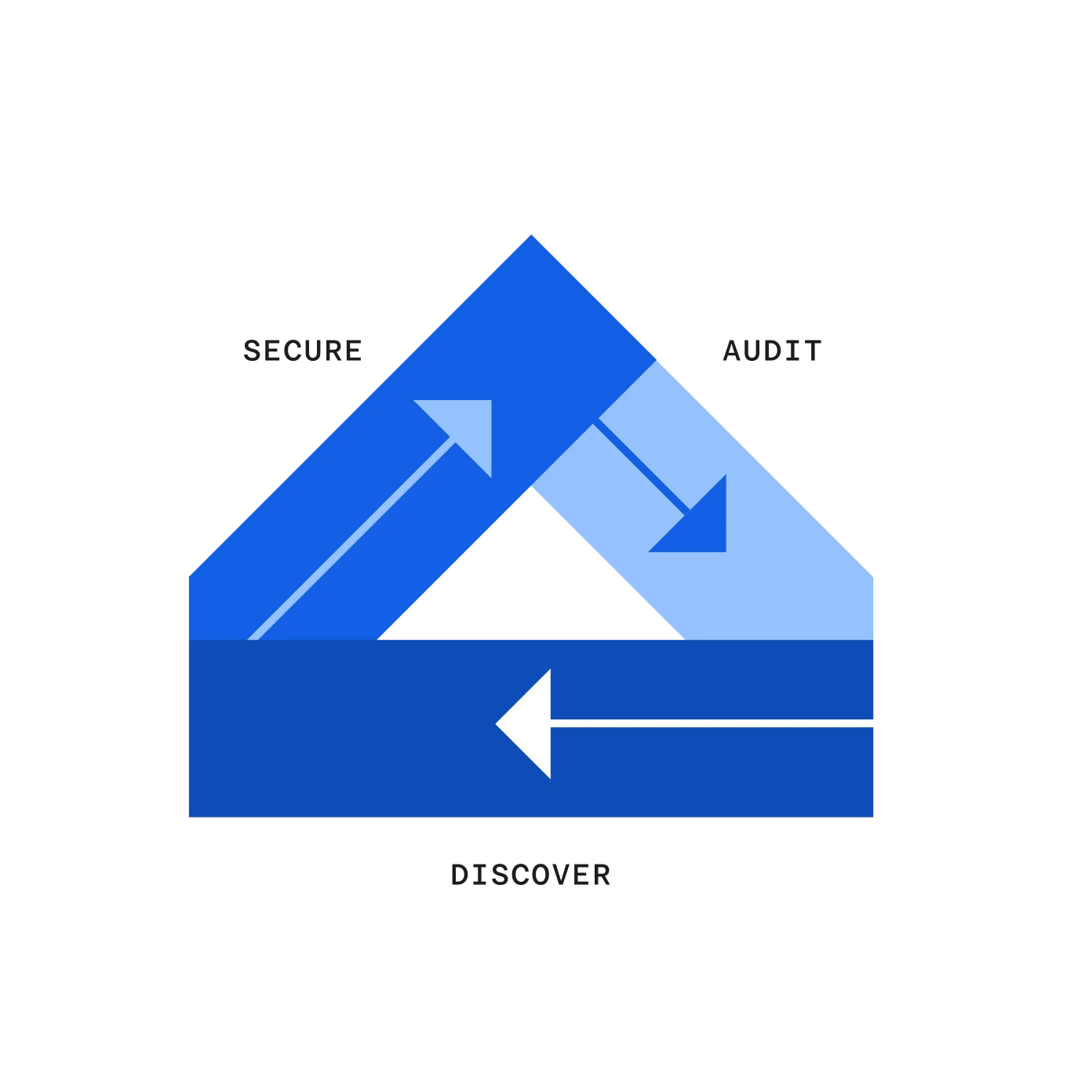
Discover who or what has access
Discover AI agents, shared credentials, and business-managed applications across your environment. Build a clear inventory of who and what has access so you can identify risk early and take action before exposure occurs.
Secure access as it happens
Vault credentials and secrets, and enforce access at the moment it happens. Apply least-privilege controls, verify device context, and govern onboarding and offboarding to ensure humans and agents only access what’s needed.
Audit every access decision
Log and explain access decisions with clear attribution across humans, machines, and agents. Generate audit trails that connect identity, device, and access activity to support investigations, demonstrate compliance, and ensure authority never outpaces control.
Secure modern work without compromise
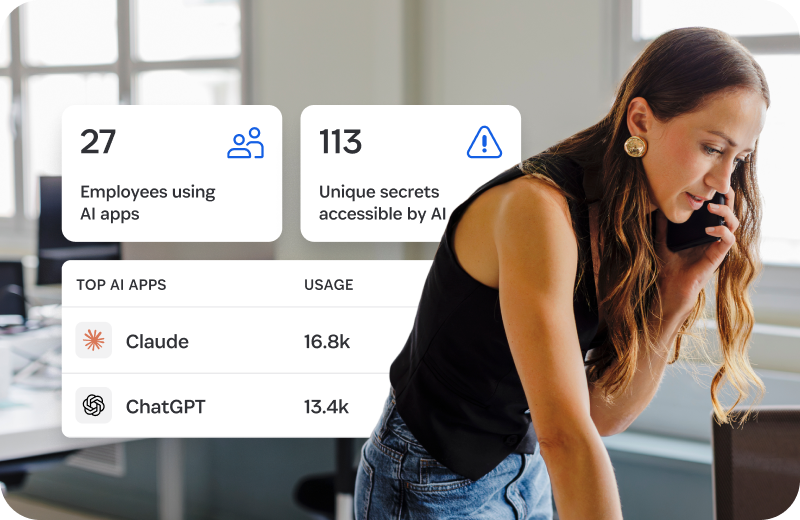
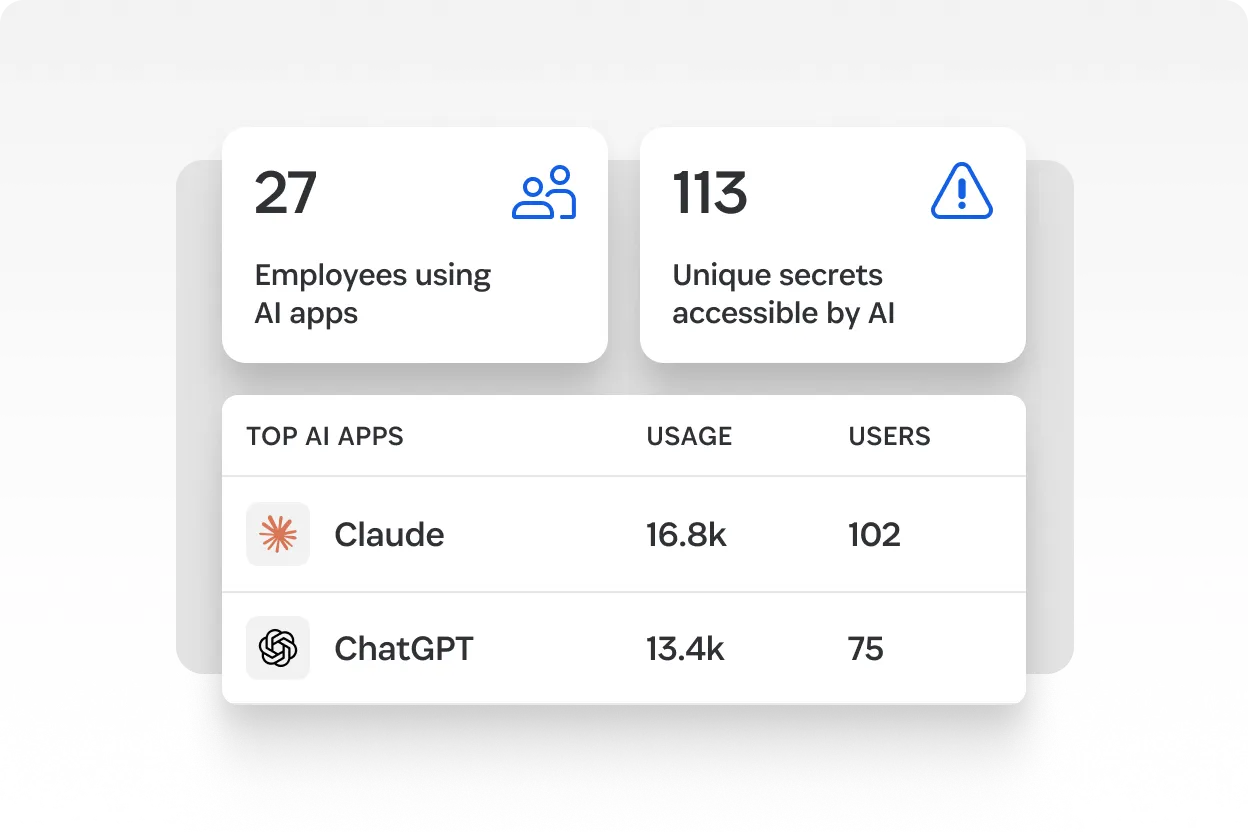
Govern AI agent access
Discover and secure AI agent access, on endpoints, in IDEs, and inside AI workflows.
Discover apps you can’t see
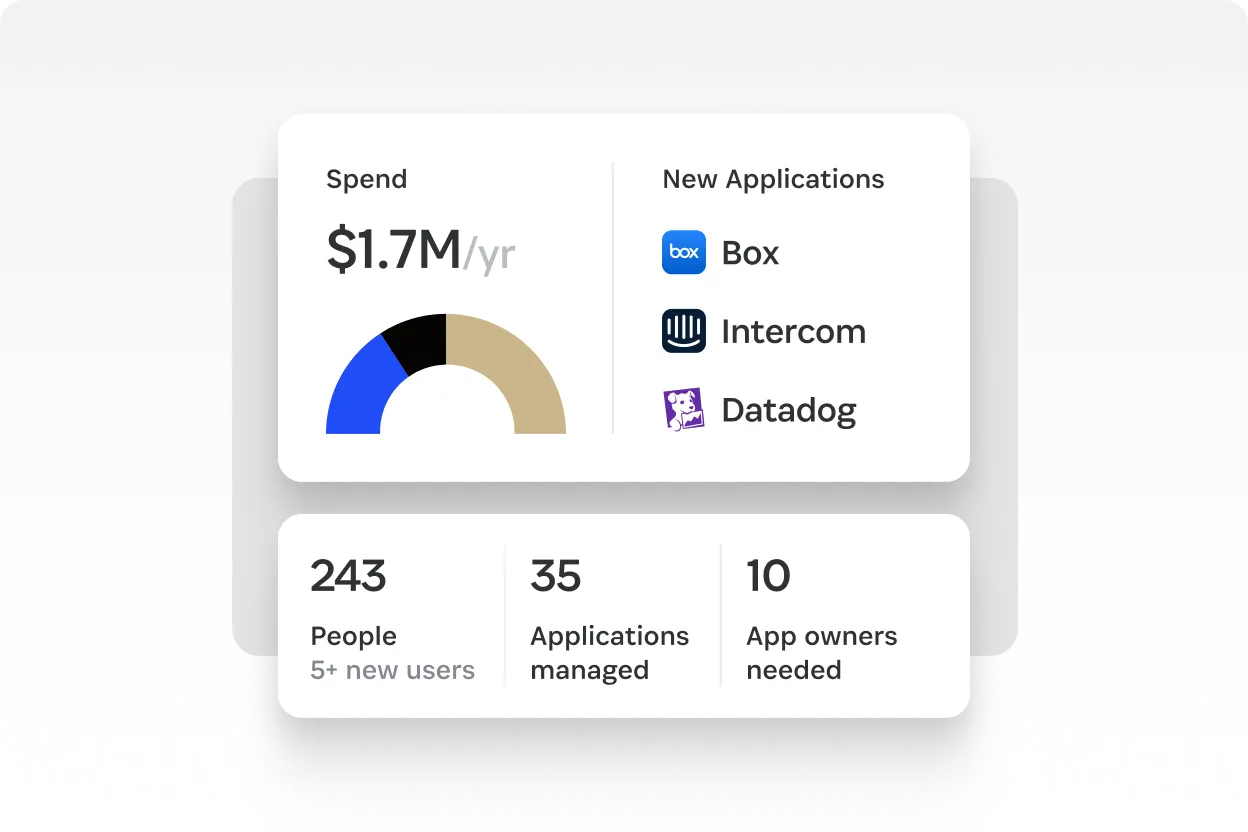
Uncover line-of-business adopted SaaS and AI tools across your environment.
Automate SaaS onboarding and offboarding
Automate joiner and leaver workflows, enforce least privilege access for apps, and optimize usage with real activity.
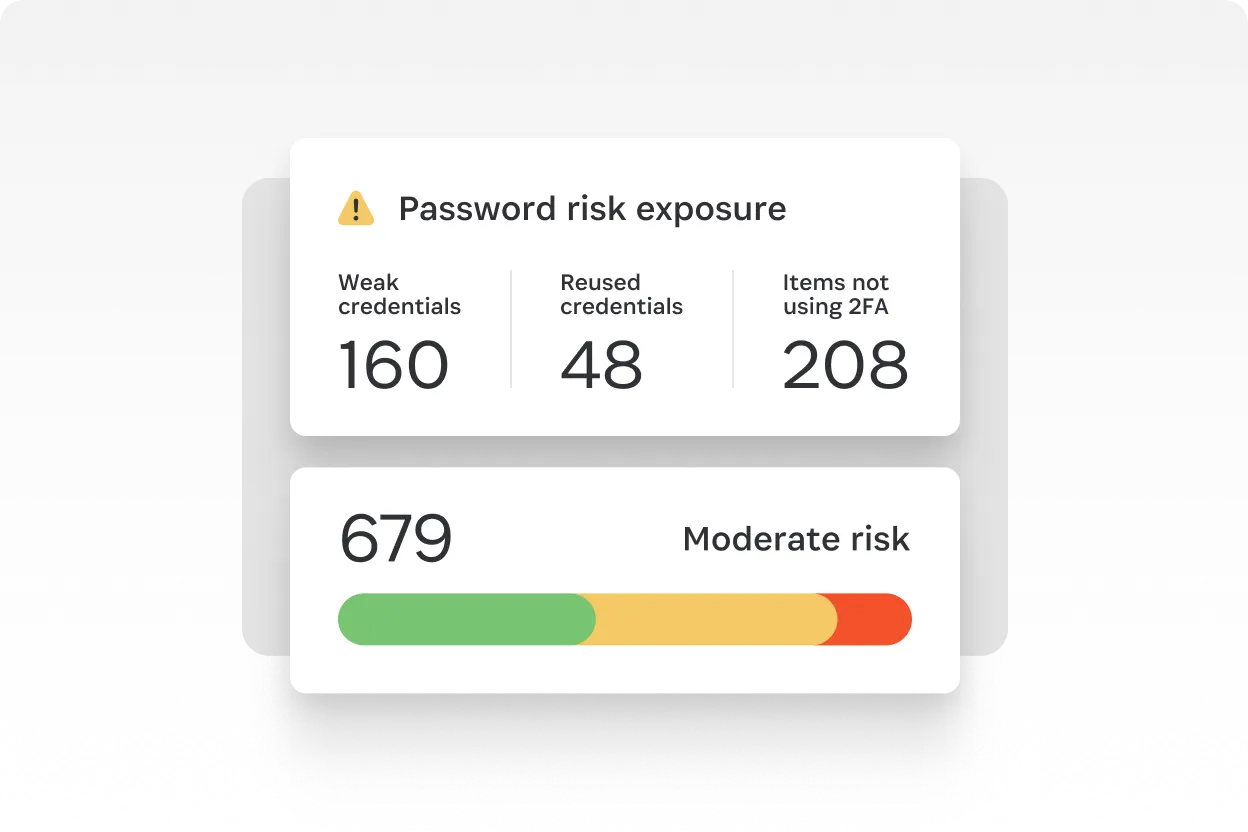
Protect human, machine, and AI credentials
Secure every password, passkey, and secret across SaaS, developers, and AI workflows. Protect what traditional providers can’t reach.
Reduce SaaS spend
Eliminate wasted SaaS spending caused by unused licenses and redundant apps while empowering your users to make informed choices.
Simplify secrets management of your team
Give DevOps teams a secure, centralized way to share and automate access to infrastructure secrets.
Our product suite
The core components of Extended Access Management
Unified Access
Unified Access brings discovery, vaulting, context-aware authorization, and auditing into one system
SaaS Manager
Discover and secure employee access to all apps, whether company-managed or business-unmanaged
Enterprise Password Manager
Secure access for employees and developers by storing passwords, passkeys, API keys, and secrets in one vault
180,000 businesses trust 1Password

“Building on the secure foundation of 1Password has allowed DMNO to create best-in-class secrets integrations for developers building agentic workflows.”
Theo Ephraim
Co-founder, DMNO
See Extended Access Management in action
See how 1Password helps you discover, secure, and audit human, machine, and AI agent access.
Extended Access Management FAQs
What is 1Password Extended Access Management?
Extended Access Management is an approach to modern identity security. It closes the Access Trust Gap created by SaaS sprawl, unmanaged credentials, endpoints outside centralized control, and a new class of identities with autonomous AI agents. Extended Access Management ensures access is continuously visible, enforced at runtime, and fully auditable across humans and non-human identities.












